In this recipe, we will create a policy that will only allow access to a service if the requestor has been authenticated as the member of a particular group. Note, that all the screens say that it is a role, but actually the mapping is to a group.
- Copy an existing policy.
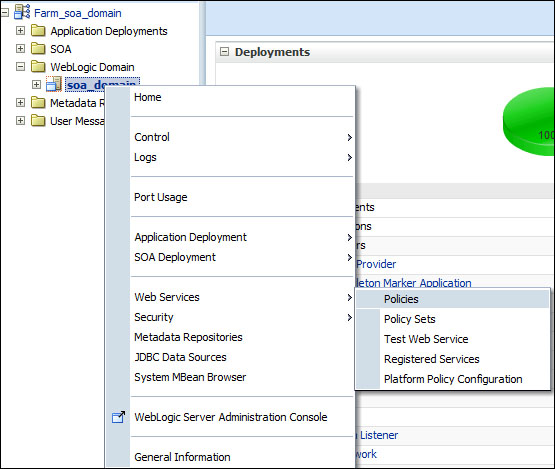
In Fusion Middleware Control, expand the Farm and WebLogic Domain, and then right-click on the domain name to bring up the menu. Select Web Services | Policies:
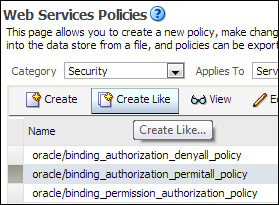
On the Web Services Policies screen, select the policy oracle/binding_authorization_permitall_policy and click on the Create Like button to make a copy of the policy:
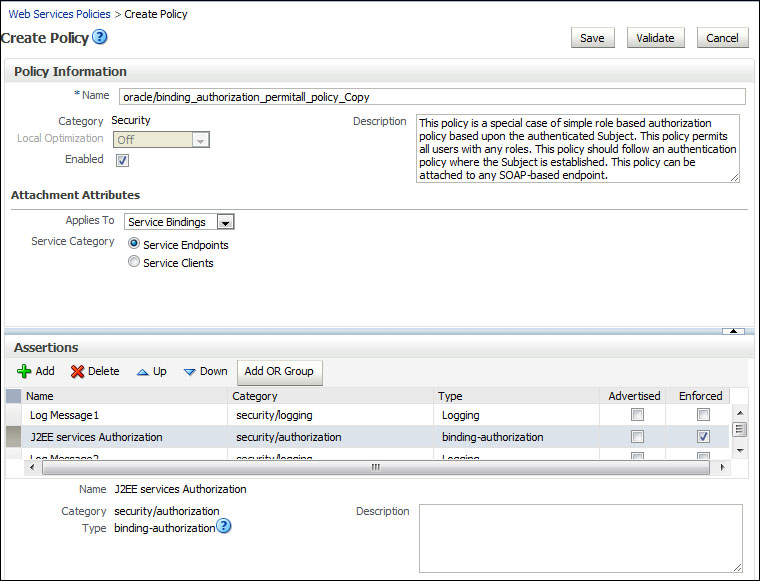
- Modify the policy.
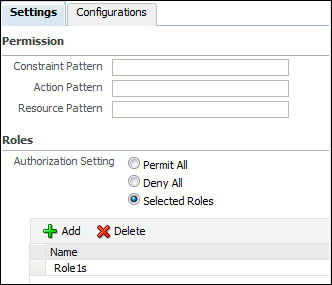
Change the Name of the policy. Accept all the default settings. In the Assertions section, select the J2EE services Authorization line, and then on the Settings tab change Roles Authorization Setting to Selected Roles. Click on the plus (
 ) sign to Add a role.
) sign to Add a role.
- Authorize a role.
Choose the group, or groups, you wish to authorize from the Roles Available list, and click on the Move arrow to move them to the Roles Selected to Add list. Then click on OK.
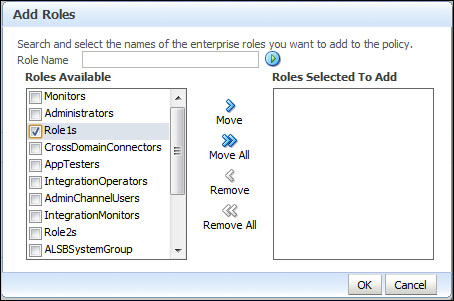
The policy may now be saved by clicking on Save.
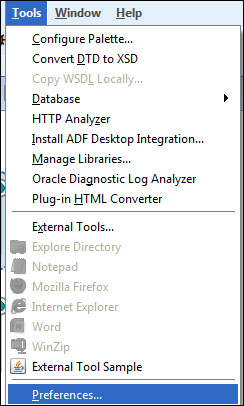
- Synchronize the policy with JDeveloper.
In order to use our new policy in JDeveloper, we must make sure that JDeveloper is retrieving the list of policies from the policy store in the WebLogic domain. To do this in JDeveloper, go to the Tools menu and select Preferences....
- Choose to synchronize with App Server.
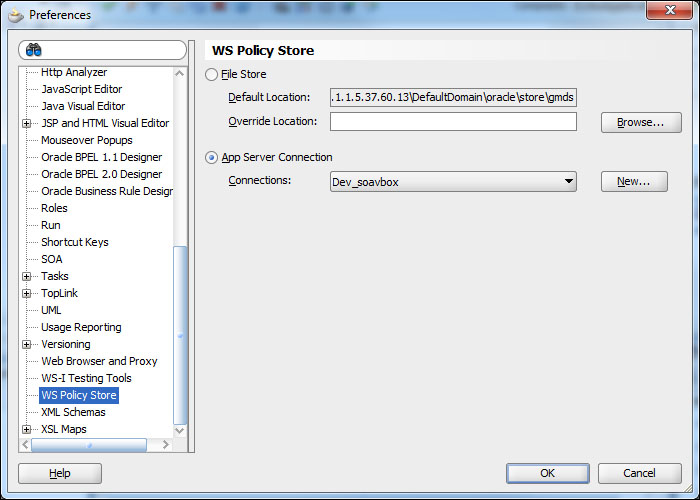
Choose the WS-Policy Store section and select the App Server Connection radio button, and choose a connection from the Connections drop-down list to the domain where you just created the new security policy. Then click on OK.
Rather than creating a new policy from scratch, we always copy an existing policy and modify it to suit our needs. Changing a policy will automatically modify the behavior of all the endpoints that are using the policy.
The authentication policy we created restricts access based on the group that a user is a member of. We created this policy in the policy store of the SOA Suite runtime environment. To make this available to JDeveloper, we could have exported the policy from the SOA Suite runtime and then imported it into JDeveloper. Instead we chose to point JDeveloper to the SOA Suite run time policy store. This has the advantage that when we add any additional policies in the future, they will automatically be available in our JDeveloper environment.
