2.6 The Playfair and ADFGX Ciphers
The Playfair and ADFGX ciphers were used in World War I by the British and the Germans, respectively. By modern standards, they are fairly weak systems, but they took real effort to break at the time.
The Playfair system was invented around 1854 by Sir Charles Wheatstone, who named it after his friend, the Baron Playfair of St. Andrews, who worked to convince the government to use it. In addition to being used in World War I, it was used by the British forces in the Boer War.
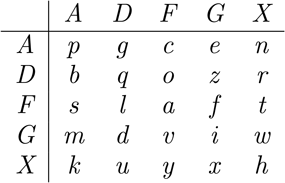
The key is a word, for example, playfair. The repeated letters are removed, to obtain playfir, and the remaining letters are used to start a matrix. The remaining spaces in the matrix are filled in with the remaining letters in the alphabet, with and being treated as one letter:
Suppose the plaintext is meet at the schoolhouse. Remove spaces and divide the text into groups of two letters. If there is a doubled letter appearing as a group, insert an and regroup. Add an extra at the end to complete the last group, if necessary. Our plaintext becomes
Now use the matrix to encrypt each two-letter group by the following scheme:
If the two letters are not in the same row or column, replace each letter by the letter that is in its row and is in the column of the other letter. For example, et becomes , since is in the same row as and the same column as , and is in the same row as and the same column as .
If the two letters are in the same row, replace each letter with the letter immediately to its right, with the matrix wrapping around from the last column to the first. For example, me becomes .
If the two letters are in the same column, replace each letter with the letter immediately below it, with the matrix wrapping around from the last row to the first. For example, becomes .
The ciphertext in our example is
To decrypt, reverse the procedure.
The system succumbs to a frequency attack since the frequencies of the various digrams (two-letter combinations) in English have been tabulated. Of course, we only have to look for the most common digrams; they should correspond to the most common digrams in English: , , , , , , . Moreover, a slight modification yields results more quickly. For example, both of the digrams and are very common. If the pairs and are common in the ciphertext, then a good guess is that , , , form the corners of a rectangle in the matrix. Another weakness is that each plaintext letter has only five possible corresponding ciphertext letters. Also, unless the keyword is long, the last few rows of the matrix are predictable. Observations such as these allow the system to be broken with a ciphertext-only attack. For more on its cryptanalysis, see [Gaines].
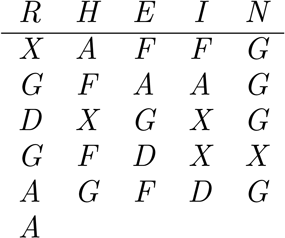
The ADFGX cipher proceeds as follows. Put the letters of the alphabet into a matrix. The letters and are treated as one, and the columns of the matrix are labeled with the letters . For example, the matrix could be
Each plaintext letter is replaced by the label of its row and column. For example, becomes , and becomes . Suppose the plaintext is
The result of this initial step is
So far, this is a disguised substitution cipher. The next step increases the complexity significantly. Choose a keyword, for example, Rhein. Label the columns of a matrix by the letters of the keyword and put the result of the initial step into another matrix:
Now reorder the columns so that the column labels are in alphabetic order:
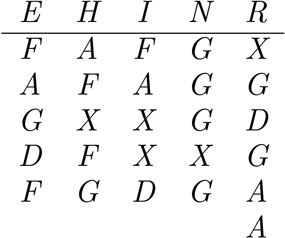
Finally, the ciphertext is obtained by reading down the columns (omitting the labels) in order:
Decryption is easy, as long as you know the keyword. From the length of the keyword and the length of the ciphertext, the length of each column is determined. The letters are placed into columns, which are reordered to match the keyword. The original matrix is then used to recover the plaintext.
The initial matrix and the keyword were changed frequently, making cryptanalysis more difficult, since there was only a limited amount of ciphertext available for any combination. However, the system was successfully attacked by the French cryptanalyst Georges Painvin and the Bureau du Chiffre, who were able to decrypt a substantial number of messages.
Here is one technique that was used. Suppose two different ciphertexts intercepted at approximately the same time agree for the first several characters. A reasonable guess is that the two plaintexts agree for several words. That means that the top few entries of the columns for one are the same as for the other. Search through the ciphertexts and find other places where they agree. These possibly represent the beginnings of the columns. If this is correct, we know the column lengths. Divide the ciphertexts into columns using these lengths. For the first ciphertext, some columns will have one length and others will be one longer. The longer ones represent columns that should be near the beginning; the other columns should be near the end. Repeat for the second ciphertext. If a column is long for both ciphertexts, it is very near the beginning. If it is long for one ciphertext and not for the other, it goes in the middle. If it is short for both, it is near the end. At this point, try the various orderings of the columns, subject to these restrictions. Each ordering corresponds to a potential substitution cipher. Use frequency analysis to try to solve these. One should yield the plaintext, and the initial encryption matrix.
The letters were chosen because their symbols in Morse code (, , , , ) were not easily confused. This was to avoid transmission errors, and represents one of the early attempts to combine error correction with cryptography. Eventually, the cipher was replaced by the cipher, which used a initial matrix. This allowed all 26 letters plus 10 digits to be used.
For more on the cryptanalysis of the ADFGX cipher, see [Kahn].
