CHAPTER 9: SOFTWARE FEATURE DESIGN RELATED TO SWID/SWEID TAG MANAGEMENT FOR TAG CREATORS AND MODIFIERS
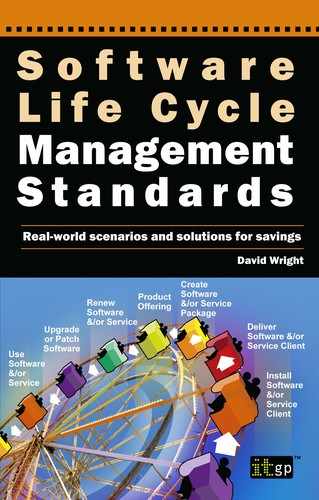
The software life cycle
Figure 49: Software/SaaS product life cycle
Figure 49 is a reminder of our life cycle. The first step in the cycle involves the process described in the following sections.
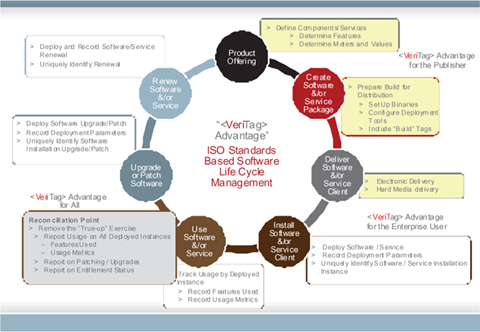
Product tagging and integration life cycle
Figure 50 is an example of the functional sequence that might be followed by a software publisher/OEM that is defining a new product.
Figure 50: Product tagging and integration sequence
A similar sequence might also be followed if the publisher/OEM has already released a product, but wishes to either:
- simply offer an application patch that updates the installation with SWID tags; or
- include application changes that require patching concurrently with updating the new patched version with SWID tags.
The example sequence shows the use of VTP and VeriTag Writer suite, but the implementer may use any set of SWID tag ISO-compliant management tools to perform the same.
How to analyse your product then design SWEID and SWID tags
The following provides an example of the analysis and design of basic static ISO SWID tags and their associated SWEID tags.
Sample software application – SoftPub Enterprise Firewall (SEF)
SoftPub is a fictitious software publisher that produces firewalls. The product contains many licensable features to which usage entitlement (a licensable for use) is offered and thus may be ultimately deployed and used. Keys are required in order to enable each feature. In order to be able to match entitlement with deployment, a unique SWID tag must be available with the deployed product in order to reconcile the deployment with licensable features.
While there are many licensing models and methods other than the one illustrated here, the approach outlined in this section may be applied to any system of entitlement and deployment.
Licence features and attributes
In the SEF products, a licence comprises several features that enable the various aspects of functionality that are available in the product. Each feature has a set of attributes that further defines the behaviour of the functionality. With the release of SEF 1.0, SoftPub provides a customer with a high degree of flexibility in ordering the SEF product features and attributes that best satisfy the needs of their organisation. Owing to the flexibility offered to the customer, the list of licensable features and their respective attributes is extensive and complex. The next few sections detail these features and attributes.
Features
The base feature for the SEF is the firewall; all other features are add-ons to the base firewall feature. Character strings that are known to both the product and the back-end configuration database represent each of the features within the SWID and SWEID tags. Tables 9 and 10 contain the lists of licensable SEF features and their respective feature strings.
Table 9: SEF base licensable features
SEF function |
Licence feature name |
Firewall |
SEF1.0-FW |
S2S |
SEF1.0-S2S |
Remote VPN |
SEF1.0-RVPN |
High availability/Load balancing |
SEF1.0-HALB |
Content filtering |
SEF1.0-CF |
Content filtering update subscription |
SEF1.0-CFS |
Table 10: SEF add-on licensable features
Add-on function |
Licence feature name |
Anti-virus |
SEF1.0-AV |
Anti-virus definition update subscription |
SEF1.0-AVS |
Intrusion detection |
SEF1.0-IDS |
Intrusion detection subscription |
SEF1.0-IDSS |
SWID tags
The feature for the SEF may be mapped directly on to a SWID tag (and by association, SWEID tag). The name of the tag is prefixed in this example by ‘swid’ in order to prevent confusion between a licensable feature name and a SWID tag. This is optional, however, and entirely up to the implementer to decide.
Table 11: SEF licensable features and corresponding SWID tag names
SEF function |
SWID tag name |
Firewall |
Swid-SEF1.0-FW |
S2S |
Swid-SEF1.0-S2S |
Remote VPN |
Swid-SEF1.0-RVPN |
High availability/Load balancing |
Swid-SEF1.0-HALB |
Swid-SEF1.0-CF |
|
Content filtering update subscription |
Swid-SEF1.0-CFS |
Add-on function |
SWID tag name |
Anti-virus |
Swid-SEF1.0-AV |
Anti-virus definition update subscription |
Swid-SEF1.0-AVS |
Intrusion detection |
Swid-SEF1.0-IDS |
Intrusion detection subscription |
Swid-SEF1.0-IDSS |
Licensable feature attributes
Each of the features listed in the previous section has several attributes. All features share many of the attributes, but the details of the attributes often differ. For example, all features have a usage count, but the usage count (meter) available for the SEF1.0-RVPN feature is not the same as the usage count of the other features.
The attributes that are available for the SEF features are:
- Usage count (meter):
- There are two types of user that are counted as part of the firewall usage count: user licences and server licences. A user licence is counted when the source IP address is from a protected interface (internal). An internal user is allowed to make as many different connections as they like, through many proxies, and this counts as a single user licence. This model is suitable for situations where internal users are trying to access the Internet. A server licence is counted when the source IP address is not from a protected interface (external).
- The type of VPN traffic is site-to-site traffic.
- Start date: this is the start date of a licence feature. Content subscription features such as content filtering and anti-virus definition updates always have a start date. All other features may have a start date. Whenever a licensed feature has an end date, it must have a start date as well.
- End date: this is the expiration date of the licensed feature. Content subscription features such as content filtering and anti-virus definition updates always have an expiration date. All other features may have an expiration date.
- Trial: if this is set then the licence is a trial licence and has a start and end date. Trial licences have an unlimited user count.
- Version: the current version of SEF is 1.0.
Table 12: SEF licensable feature attributes
Licence feature name |
Feature attributes |
SWID tag attributes |
SEF1.0-FW |
Usage count |
25, 50, 100, 250, (unlimited) |
|
Start date |
Start date or <empty> |
|
End date |
Licence expiration date. Typically an empty string – |
|
unlimited |
|
|
Version |
1.0 |
|
Trial |
1 if trial, 0 otherwise |
|
Accreditation |
<empty> or <organisation> |
SEF1.0-S2S |
Usage count |
(unlimited) |
|
Start date |
Start date or <empty> |
|
End date |
Licence expiration date. Typically an empty string – unlimited |
|
Version |
1.0 |
|
Trial |
1 if trial, 0 otherwise |
|
Accreditation |
<empty> or <organisation> (if site licence) |
SEF1.0-RVPN |
Usage count |
5, 25, 100, 250, (unlimited) |
|
Start date |
Start date or <empty> |
|
End date |
Licence expiration date. Typically an empty string – unlimited |
|
Version |
1.0 |
|
Trial |
1 if trial, 0 otherwise |
|
Accreditation |
<empty> or <organisation> |
SEF1.0-HALB |
Usage count |
(unlimited) |
Start date |
Start date or <empty> |
|
|
End date |
Licence expiration date. Typically an empty string – unlimited |
|
Version |
1.0 |
|
Trial |
1 if trial, 0 otherwise |
|
Accreditation |
<empty> or <organisation> |
SEF1.0-CF |
Usage count |
25, 50, 100, 250, (unlimited) |
|
Start date |
Start date or <empty> |
|
End date |
Licence expiration date. Typically an empty string – unlimited |
|
Version |
1.0 |
|
Trial |
1 if trial, 0 otherwise |
|
Accreditation |
<empty> or <organisation> |
SEF1.0-CFS |
Usage count |
25, 50, 100, 250, (unlimited) |
|
Start date |
Start date |
|
End date |
Subscription expiration date |
|
Hostid |
<hostid> or <empty> (if site licence) |
|
Version |
1.0 |
Trial |
1 if trial, 0 otherwise |
|
|
Accreditation |
<empty> or <organisation> |
SEF1.0-AV |
Usage count |
25, 50, 100, 250, (unlimited) |
|
Start date |
Start date or <empty> |
|
End date |
Licence expiration date. Typically an empty string – unlimited |
|
Version |
1.0 |
|
Trial |
1 if trial, 0 otherwise |
|
Accreditation |
<empty> or <organisation> |
SEF1.0-AVS |
Usage count |
25, 50, 100, 250, (unlimited) |
|
Start date |
Start date |
|
End date |
Subscription expiration date |
|
Version |
1.0 |
|
Trial |
1 if trial, 0 otherwise |
|
Accreditation |
<empty> or <organisation> (if site licence) |
SEF1.0-IDS |
|
25, 50, 100, 250, SLIC_METERCOUNT_MAX (unlimited) |
|
Start date |
Start date or <empty> |
End date |
Licence expiration date. Typically and empty string – unlimited |
|
|
Version |
1.0 |
|
Trial |
1 if trial, 0 otherwise |
|
Accreditation |
<empty> or <organisation> |
SEF1.0-IDSS |
Usage count |
25, 50, 100, 250, SLIC_METERCOUNT_MAX (unlimited) |
|
Start date |
Start date |
|
End date |
Subscription expiration date |
|
Version |
1.0 |
|
Trial |
1 if trial, 0 otherwise |
|
Accreditation |
<empty> or <organisation> |
Design a SWID tag
Consider the single licensable feature SEF1.0-FW, the base firewall feature.
Table 13: SEF base firewall feature
Licence feature name |
Feature attributes |
SWID tag attributes |
SEF1.0-FW |
Usage count |
25, 50, 100, 250, (unlimited) |
Start date |
Start date or <empty> |
|
|
End date |
Licence expiration date. Typically an empty string – unlimited |
|
Version |
1.0 |
|
Trial |
1 if trial, 0 otherwise |
In order to differentiate between the multiple meter values, the publisher may choose to create a separate tag for each meter, i.e. perhaps SEF1.0-FW-25, SEF1.0-FW-50 and so on. Alternatively, these values may be defined in an extended_information tag element as defined by ISO.
Consider the elements of a SWID tag.
Table 14: Elements of a SWID tag
A tool such as VTP might be used to define the elements within the SWID tag as shown in Figure 51.
Figure 51: VeriTag Publisher screenshot
This allows input of element data, generation of a SWID tag and subsequent validation of the SWID tag to the level required:
- no certification
- basic certification
- TagVault.org SAM certification.
The resulting SWID tag might look as shown in Figure 52.
<?xml version="1.0" encoding="UTF-8"?>
<swid:software_identification_tag id="idvalue0"
xmlns:ds= "http://www.w3.org/2000/09/xmldsig#"
xmlns:swid="http://standards.iso.org/iso/19770/-2/2009/schema.xsd"
xmlns:xsi="http://www.w3.org/2001/XMLSchema-instance"
xsi:schemaLocation= "http://standards.iso.org/iso/19770/-2/2009/schema.xsd
swid.xsd">
<swid:entitlement_required_indicator
id="idvalue1">true</swid:entitlement_required_indicator>
<swid:product_title id="idvalue2" xsi:type="swid:Token">SoftPub Enterprise
Firewall V1.0</swid:product_title>
<swid:product_version id="idvalue3">
<swid:name id="idvalue4" xsi:type="swid:Token">token</swid:name>
<swid:numeric id="idvalue5">
<swid:major id="idvalue6">1</swid:major>
<swid:minor id="idvalue7">0</swid:minor>
<swid:build id="idvalue8">0</swid:build>
<swid:review id="idvalue9">0</swid:review>
</swid:numeric>
</swid:product_version>
<swid:software_creator id="idvalue10">
<swid:name id="idvalue11" xsi:type="swid:Token">SoftPub
Corporation</swid:name>
<swid:regid id="idvalue12">www.softpub.com</swid:regid>
</swid:software_creator>
<swid:software_licensor id="idvalue13">
<swid:name id="idvalue14" xsi:type="swid:Token">SoftPub
Corporation”</swid:name>
<swid:regid id="idvalue15">www.softpub.com</swid:regid>
</swid:software_licensor>
<swid:software_id id="idvalue16">
<swid:unique_id id="idvalue17" xsi:type="swid:Token">fc3cc419-b5a1-9f16-ed203e537c40</swid:unique_id>
<swid:tag_creator_regid
id="idvalue18">www.softpub.com</swid:tag_creator_regid>
</swid:software_id>
<swid:tag_creator id="idvalue19">
<swid:name id="idvalue20" xsi:type="swid:Token">SoftPub
Corporation</swid:name>
<swid:regid id="idvalue21">www.softpub.com</swid:regid>
</swid:tag_creator>
<swid:abstract id="idvalue22" lang="en">This is the base feature for the SEF
and is the firewall; all other features are add-ons to the base firewall
feature</swid:abstract>
<swid:component_of id="idvalue23">
<swid:software_id id="idvalue24">
<swid:unique_id id= "idvalue25"
xsi:type="swid:Token">token</swid:unique_id>
<swid:tag_creator_regid id="idvalue26">token</swid:tag_creator_regid>
</swid:software_id>
</swid:component_of>
<swid:complex_of id="idvalue27">
<swid:software_id id="idvalue28">
<swid:unique_id id="idvalue29" xsi:type="swid:Token">fc3cc419-b5a1-9f16-ed203e537c40</swid:unique_id>
<swid:tag_creator_regid
id="idvalue30">www.softpub.com</swid:tag_creator_regid>
</swid:software_id>
<swid:software_id>
<swid:unique_id>fc3cc419-b5a1-9f16-ed203e537c41</swid:unique_id>
<swid:tag_creator_regid>www.softpub.com</swid:tag_creator_regid>
</swid:software_id>
<swid:software_id>
<swid:unique_id>fc3cc419-b5a1-9f16-ed203e537c42</swid:unique_id>
<swid:tag_creator_regid>www.softpub.com</swid:tag_creator_regid>
</swid:software_id>
<swid:unique_id>fc3cc419-b5a1-9f16-ed203e537c43</swid:unique_id>
<swid:tag_creator_regid>www.softpub.com</swid:tag_creator_regid>
</swid:software_id>
<swid:software_id>
<swid:unique_id>fc3cc419-b5a1-9f16-ed203e537c44</swid:unique_id>
<swid:tag_creator_regid>www.softpub.com</swid:tag_creator_regid>
</swid:software_id>
<swid:software_id>
<swid:unique_id>fc3cc419-b5a1-9f16-ed203e537c45</swid:unique_id>
<swid:tag_creator_regid>www.softpub.com</swid:tag_creator_regid>
</swid:software_id>
<swid:software_id>
<swid:unique_id>fc3cc419-b5a1-9f16-ed203e537c46</swid:unique_id>
<swid:tag_creator_regid>www.softpub.com</swid:tag_creator_regid>
</swid:software_id>
<swid:software_id>
<swid:unique_id>fc3cc419-b5a1-9f16-ed203e537c47</swid:unique_id>
<swid:tag_creator_regid>www.softpub.com</swid:tag_creator_regid>
</swid:software_id>
<swid:software_id>
<swid:unique_id>fc3cc419-b5a1-9f16-ed203e537c48</swid:unique_id>
<swid:tag_creator_regid>www.softpub.com</swid:tag_creator_regid>
</swid:software_id>
<swid:software_id>
<swid:unique_id>fc3cc419-b5a1-9f16-ed203e537c49</swid:unique_id>
<swid:tag_creator_regid>www.softpub.com</swid:tag_creator_regid>
</swid:software_id>
</swid:complex_of>
<swid:data_source id= "idvalue31"
xsi:type="swid:Token">token</swid:data_source>
<swid:dependency id="idvalue32">
<swid:software_id id="idvalue33">
<swid:unique_id id= "idvalue34"
xsi:type="swid:Token">token</swid:unique_id>
<swid:tag_creator_regid id="idvalue35">token</swid:tag_creator_regid>
</swid:software_id>
</swid:dependency>
<swid:elements_owner id="idvalue36">
<swid:owner_name id="idvalue37"
xsi:type="swid:Token">token</swid:owner_name>
<swid:owner_regid id="idvalue38">token</swid:owner_regid>
<swid:element_id id="idvalue39">idvalue0</swid:element_id>
</swid:elements_owner>
<swid:installation_details id="idvalue40">
<swid:location_platform id="idvalue41"
xsi:type="swid:Token">token</swid:location_platform>
<swid:location_installation id="idvalue42"
xsi:type="swid:Token">token</swid:location_installation>
<swid:installation_instance id= "idvalue43"
xsi:type="swid:Token">token</swid:installation_instance>
<swid:installation_locale id="idvalue44"
xsi:type="swid:Token">token</swid:installation_locale>
<swid:installation_target_id id= "idvalue45"
xsi:type="swid:Token">token</swid:installation_target_id>
</swid:installation_details>
<swid:keywords id="idvalue46">
<swid:keyword id="idvalue47" xsi:type="swid:Token">token</swid:keyword>
</swid:keywords>
<swid:license_linkage id="idvalue48">
<swid:activation_status id= "idvalue49"
xsi:type="swid:Token">token</swid:activation_status>
<swid:channel_type id= "idvalue50"
xsi:type="swid:Token">token</swid:channel_type>
<swid:channel_name id= "idvalue51"
xsi:type="swid:Token">token</swid:channel_name>
<swid:customer_type id= "idvalue52"
xsi:type="swid:Token">token</swid:customer_type>
</swid:license_linkage>
<swid:package_footprint id="idvalue53">
<swid:external_description
id="idvalue54">http://tempuri.org</swid:external_description>
</swid:package_footprint>
<swid:packager id="idvalue55">
<swid:by id="idvalue56" xsi:type="swid:Token">token</ swid:by>
<swid:part id="idvalue57" xsi:type="swid:Token">token</swid:part>
</swid:packager>
<swid:product_category id="idvalue58">
<swid:UNSPSC_ver id= "idvalue59"
xsi:type="swid:Token">token</swid:UNSPSC_ver>
<swid:segment_title id= "idvalue60"
xsi:type="swid:Token">token</swid:segment_title>
<swid:family_title id="idvalue61"
xsi:type="swid:Token">token</swid:family_title>
<swid:class_title id="idvalue62"
xsi:type="swid:Token">token</swid:class_title>
<swid:commodity_title id="idvalue63"
xsi:type="swid:Token">token</swid:commodity_title>
<swid:code id="idvalue64">0</swid:code>
</swid:product_category>
<swid:product_family id= "idvalue65"
xsi:type="swid:Token">token</swid:product_family>
<swid:product_id id="idvalue66" xsi:type="swid:Token">fc3cc419-b5a1-9f16-ed203e537c40</swid:product_id>
<swid:release_date id="idvalue67">2001-12-
31T12:00:00</swid:release_date>
<swid:release_id id="idvalue68" xsi:type="swid:Token">token</ swid:release_id>
<swid:release_package id="idvalue69">
<swid:sign_off id="idvalue70" xsi:type="swid:Token">token</swid:sign_off>
<swid:sign_off_date id="idvalue71">2001-12-
31T12:00:00</swid:sign_off_date>
<swid:by id="idvalue72" xsi:type="swid:Token">token</ swid:by>
</swid:release_package>
<swid:release_rollout id="idvalue73">
<swid:sign_off id="idvalue74" xsi:type="swid:Token">token</swid:sign_off>
<swid:sign_off_date id="idvalue75">2001-12-
31T12:00:00</swid:sign_off_date>
<swid:by id="idvalue76" xsi:type="swid:Token">token</ swid:by>
</swid:release_rollout>
<swid:release_verification id="idvalue77">
<swid:sign_off id="idvalue78" xsi:type="swid:Token">token</swid:sign_off>
<swid:sign_off_date id="idvalue79">2001-12-
31T12:00:00</swid:sign_off_date>
<swid:by id="idvalue80" xsi:type="swid:Token">token</ swid:by>
</swid:release_verification>
<swid:serial_number id= "idvalue81"
xsi:type="swid:Token">E12345678</swid:serial_number>
<swid:sku id="idvalue82" xsi:type="swid:Token">SEF-1P0-EDU-25</swid:sku>
<swid:software_creator_alias id="idvalue83">
<swid:alias id="idvalue84">
<swid:alias_name id="idvalue85"
xsi:type="swid:Token">token</swid:alias_name>
<swid:alias_regid id="idvalue86">token</swid:alias_regid>
</swid:alias>
</swid:software_creator_alias>
<swid:software_licensor_alias id="idvalue87">
<swid:alias id="idvalue88">
<swid:alias_name id= "idvalue89"
xsi:type="swid:Token">token</swid:alias_name>
<swid:alias_regid id="idvalue90">token</swid:alias_regid>
</swid:alias>
</swid:software_licensor_alias>
<swid:supported_languages id="idvalue91">
<swid:language id="idvalue92" xsi:type="swid:Token">token</swid:language>
</swid:supported_languages>
<swid:tag_creator_alias id="idvalue93">
<swid:alias id="idvalue94">
<swid:alias_name id= "idvalue95"
xsi:type="swid:Token">token</swid:alias_name>
<swid:alias_regid id="idvalue96">token</swid:alias_regid>
</swid:alias>
</swid:tag_creator_alias>
<swid:tag_creator_copyright id="idvalue97"
lang="en">swid:tag_creator_copyright</swid:tag_creator_copyright>
<swid:tag_version id="idvalue98">
<swid:name id="idvalue99" xsi:type="swid:Token">token</swid:name>
<swid:regid id="idvalue100">token</swid:regid>
<swid:numeric_version id="idvalue101">
<swid:numeric id="idvalue102">0</swid:major>
<swid:minor id="idvalue103">0</swid:minor>
<swid:build id="idvalue104">0</swid:build>
<swid:review id="idvalue105">0</swid:review>
</swid:numeric_version>
</swid:tag_version>
<swid:upgrade_for id="idvalue106">
<swid:upgrade_id id="idvalue107">
<swid:unique_id id= "idvalue108"
xsi:type="swid:Token">token</swid:unique_id>
<swid:tag_creator_regid id="idvalue109">token</swid:tag_creator_regid>
</swid:upgrade_id>
<swid:upgrade_description id= "idvalue110"
xsi:type="swid:String">swid:upgrade_description</swid:upgrade_description>
</swid:upgrade_for>
<swid:usage_identifier id="idvalue111">
<swid:filename id="idvalue112" xsi:type="swid:Token">token</swid:filename>
<swid:processname id="idvalue113" type="literal">token</swid:processname>
<swid:URI id="idvalue114" type="literal">token</swid:URI>
</swid:usage_identifier >
<swid:validation id="idvalue115">
<swid:validation_call id="idvalue116"
xsi:type="swid:Token">token</swid:validation_call>
<swid:last_validated_by id="idvalue117"
xsi:type="swid:Token">token</swid:last_validated_by>
<swid:last_validated_date id="idvalue118">2001-12-
31T12:00:00</swid:last_validated_date>
<swid:last_validated_result id= "idvalue119"
xsi:type="swid:Token">token</swid:last_validated_result>
</swid:validation>
<ds:Signature Id="idvalue120">
<ds:SignedInfo Id= "idvalue121">
<ds:CanonicalizationMethod Algorithm="http://tempuri.org"/>
<ds:SignatureMethod Algorithm="http://tempuri.org">
<ds:HMACOutputLength>0</ds:HMACOutputLength>
</ds:SignatureMethod>
<ds:Reference Id="idvalue122" Type="http://tempuri.org"
URI="http://tempuri.org">
<ds:Transforms>
<ds:Transform Algorithm="http://tempuri.org">
<ds:XPath>ds:XPath</ds:XPath>
</ds:Transform>
</ds:Transforms>
<ds:DigestMethod Algorithm="http://tempuri.org"/>
<ds:DigestValue>0</ds:DigestValue>
</ds:Reference>
</ds:SignedInfo>
<ds:SignatureValue Id="idvalue123">0</ds:SignatureValue>
<ds:KeyInfo Id="idvalue124">
<ds:KeyName>ds:KeyName</ds:KeyName>
</ds:KeyInfo>
<ds:Object Encoding="http://tempuri.org" Id="idvalue125" MimeType="">
<ds:SPKIData>
<ds:SPKISexp>0</ds:SPKISexp>
</ds:SPKIData>
</ds:Object>
</ds:Signature>
<swid:extended_information id="idvalue126"/>
</swid:software_identification_tag>
Figure 52: SWID base tag
The resulting SWID tag should be verified with TagVault.org as compliant and entered in the TagVault.org tag registry.
How to use the tags
Step two in our life cycle, the ‘Create Software &/or Service Package’ step in Figure 4, involves injecting the initial SWID tags, sometimes referred to as build tags, into the build or ‘bag of bits’.
These SWID tags then become available for insertion into the consumer infrastructure at install/deployment time, the ‘Install Software &/or Service Client’ step in Figure 4.
The third step in the cycle, the ‘Deliver Software &/or Service Client’ step in Figure 4, requires that automation be added to the delivery infrastructure, either as a custom step or via acquisition from the many companies now engaging in ISO/IEC 19770 technology.
Figure 53: VeriTag Publisher architecture
Figure 53 shows a very high-level architectural view of what this means.
The fulfilment/delivery infrastructure may be interfaced to deliver both SWID and SWEID tags.
The SWEID tag
SWEID tags are created and delivered as a result of some business transaction performed possibly by the ERP (sales of a licensed SKU) or perhaps a customised buying programme infrastructure that issues entitlements according to some contract.
Each SWEID tag may be uniquely identified (using the paradigms described earlier) and indexed back to the transaction within the publisher’s infrastructure. In order to assist the consumer, perhaps a reference number provided by the consumer during the business transaction might be included in the SWEID tag.
At this point, both consumer and creator have a standard record of the entitlement instance, which can be referenced in either infrastructure.
The SWID tag
The SWID tag(s) will be delivered as part of the distribution ‘bag of bits’. Conceivably the tag will be the build tag only; however, it is possible that the build tag might form a prototype for a uniquely identifiable SWID tag that is indexed to the generation or delivery (especially in the case of ESD) of the distribution. This delivery may in itself be indexed back to the business transaction, allowing at least partial matching of subsequent deployments of the distribution to the business transaction.
Allowing measurement of usage with SWID tags
There is a paradigm of SWID tagging whereby the SWID tag is extended, using the ISO/IEC 19770-2:2009 definition, to capture true usage information. The technique works with both SaaS client and licensed software, and requires active participation of the installed software.
Symantec will be introducing this type of functionality with their products in the near future. Measurement of usage will include basic activity plus metrics and feature use over time.