Chapter 7
Industrial Espionage in Cyberspace
Chapter Objectives
After reading this chapter and completing the exercises, you will be able to do the following:
 Understand what is meant by industrial espionage
Understand what is meant by industrial espionage Explain the dangers of industrial espionage
Explain the dangers of industrial espionage Understand the low-technology methods used to attempt industrial espionage
Understand the low-technology methods used to attempt industrial espionage Be aware of how spyware is used in espionage
Be aware of how spyware is used in espionage Know how to protect a system from espionage
Know how to protect a system from espionage
Introduction
Espionage is not just for nation-states. Corporations have valuable intellectual property. Whether it is trade secrets, marketing data, or pending financial moves, this data can be quite valuable—and this brings us to the topic of industrial espionage. When you hear the word espionage, perhaps you may conjure up a number of exciting and glamorous images. Perhaps you have visions of a well-dressed man who drinks martinis, shaken but not stirred, traveling to glamorous locations with equally glamorous travel companions. Or perhaps you envision some exciting covert operation with highspeed car chases and guns blazing in faraway exotic lands. Espionage is often much less exciting than those popular media portrayals. The ultimate goal of espionage is to obtain information that would not otherwise be available. Generally, espionage is best done with as little fanfare as possible. Information is the goal, and blazing gun battles and glamorous locations are unlikely and would result in unwanted attention. If possible, it is best to obtain information without the target organization realizing that its information has been compromised.
Some people assume that such spying is only engaged in by governments, intelligence agencies (such as the CIA, NSA, MI6, FSB, and so on), and nefarious international organizations, such as Al-Qaida or ISIS. While those entities absolutely engage in espionage, they are certainly not the only organizations that do so. The aforementioned organizations desire to acquire information for political and military goals. As previously discussed, corporations can have valuable information. With billions of dollars at stake, a private company can become engaged in industrial espionage as either a target or a perpetrator. What company would not like to know exactly what its competitor is doing? In fact, corporate or economic espionage is on the rise.
The boundary between industrial espionage and the activities of intelligence agencies is becoming blurred. There have been numerous cases of industrial espionage against Western nations that at least appear to have been supported by foreign intelligence services. Tech companies have often been the targets of such attacks. In fact, there have been multiple warnings of nation-state actors targeting companies. In May 2022, the New York Law Journal published an article about nation-state actors using cyber attacks to go after sensitive information of corporations.1
1. https://www.law.com/newyorklawjournal/2022/05/06/%C2%AD%C2%AD%C2%AD%C2%AD%C2%AD%C2%AD%C2%AD%C2%AD%C2%AD%C2%AD%C2%AD%C2%ADnation-state-sponsored-attacks-not-your-grandfathers-cyber-attacks/?slreturn=20220626171326
While most experts believe that corporate espionage is a substantial problem, it can be difficult to assess how big the problem is. Companies that perpetrate corporate espionage do not share the fact that they do it—for obvious reasons. Companies that are victims of such espionage often do not wish to reveal that fact either. Revealing that their security was compromised could have a negative impact on their stock value. It is also possible, in certain cases, that such a breach of security might open a company to liability claims from customers whose data may have been compromised. And in some cases, the victim might not be aware of the breach. For these reasons, companies often are hesitant to disclose any industrial espionage activities. Because you will want to protect yourself and your company, it is important that you learn about espionage methods and protections. In the exercises at the end of this chapter, you will work with some of the tools you have learned about so far in this book—antispyware, key loggers, and screen-capture software—so that you can learn how they work and, hence, become cognizant of the risks they pose.
In May 2022, Xiaorong You of Lansing, Michigan, was convicted of conspiring to commit trade secret theft, economic espionage, wire fraud, and other charges. In this case, the secrets at issue involved formulations for coatings inside beverage cans. You was accused of stealing the secrets for use in setting up a new company in China.2 In 2019, Forbes ran an article on spying incidents at Apple Inc.3 In the cases examined in this article, the line between corporate espionage and state-sponsored spying was blurry. In one of the cases, Apple employee Jizhong Chen was accused of stealing trade secrets related to self-driving cars and providing them to the Chinese government. The same article estimated the cost of corporate espionage at $1.1 trillion per year.
2. https://www.justice.gov/opa/pr/chemist-sentenced-stealing-trade-secrets-economic-espionage-and-wire-fraud
3. https://www.forbes.com/sites/betsyatkins/2019/02/12/learning-from-apples-spying-incidents-how-to-protect-your-company-from-corporate-espionage/#54d18f7d6fb4
This is a global problem. In 2021 a Swedish court convicted Kristian Dimitrievski of stealing confidential information from truck and bus manufacturer Scania and selling that information to a Russian diplomat.4
4. https://apnews.com/article/europe-business-russia-espionage-stockholm-9cbf938ce9dca9a7cffb8c30be29f857
What Is Industrial Espionage?
Industrial espionage is the use of spying techniques to find out key information that is of economic value. Such data might include details on a competitor’s new project, a list of a competitor’s clients, research data, or any information that might give the spying organization an economic advantage. While the rationale for corporate espionage is different from the rationale for military espionage, corporate espionage often involves the same techniques employed by intelligence agencies, such as monitoring, photocopying files, or compromising a member of the target organization. Not only does economic espionage use the same techniques as intelligence agencies, but it often also uses the same people. There have been a number of incidents in which former intelligence agents have been found working in corporate espionage. When such individuals bring their skills and training to the world of corporate espionage, the situation becomes especially difficult for computer security experts.
In Practice
Leaving with Sensitive Data
While various computer experts and government agencies attempt to estimate the impact and spread of corporate espionage, its very nature makes accurate estimates impossible. Not only do the perpetrators not wish to disclose their crimes but often the victims will not disclose the events either. However, anecdotal evidence would suggest that the most common form of espionage is simply an employee quitting, taking a job with another firm, and leaving the first firm with sensitive data. In many cases, these employees choose data that is readily available within the company and, as such, the confidentiality of this data is considered a “gray area.” For example, a salesperson might leave with a printout of contacts and customers so that he can solicit them on behalf of the next employer.
It is critical that you have a very well-worded nondisclosure and noncompete agreement with all employees. It is best to solicit the services of an employment attorney to draw up this agreement. Additionally, you might consider limiting an employee’s access to data prior to terminating his employment. You should also conduct exit interviews and consider confiscating items such as company phone books, which may at first seem insignificant but could contain data that would be useful to another company. Also, thumb drives, smart phones, and other technologies provide a method for taking data out of a company, so some companies restrict the use of these devices.
Information as an Asset
Many people are used to viewing tangible objects as assets but have difficulty appreciating that information can be an asset. Companies spend billions of dollars every year on research and development. The discovered information is worth at least the amount of resources taken to derive the information plus the economic gain produced by the information. For example, if a company spends $200,000 researching a process that will in turn generate $1 million in revenue, then that data is worth at least $1.2 million. You can think of this economic gain as a simple equation:
VI (Value of Information) = C (Cost to Produce) + VG (Value Gained)
While some people are not yet fully cognizant of the concept, data does indeed represent a valuable asset. When we speak of the “information age” or our “information-based economy,” it is important to realize that these terms are not just buzzwords. Information is a real commodity. It is as much an economic asset as any other item in a company’s possession. In fact, it is most often the case that the data residing on a company’s computer is worth far more than the hardware and software of the computer system itself. It is certainly the case that the data is much more difficult to replace than the computer hardware and software.
To truly appreciate the concept of information as a commodity, consider the process of earning a college degree. You spend 4 years sitting in various classrooms. You pay a significant amount of money for the privilege of sitting in those rooms, and listening to others speak at length on various topics. At the end of the 4 years, the only tangible product you receive is a single piece of paper. Surely you can get a piece of paper for far less cost and with much less effort. What you actually paid for was the information you received. The same is true of the value of many professions. Doctors, attorneys, engineers, consultants, managers, and so forth all are consulted for their expert information. Information itself is the valuable commodity.
The data stored in computer systems has a high value for two reasons. First, a great deal of time and effort go into creating and analyzing the data. If you spend 6 months with a team of five people gathering and analyzing information, then that information is worth at least an amount equal to the salaries and benefits of those people for that length of time. Second, data often has intrinsic value, apart from the time and effort spent acquiring those facts. If the facts are about a proprietary process, invention, or algorithm, the value is obvious. However, any data that might provide a competitive edge is inherently valuable. For example, insurance companies frequently employ teams of statisticians and actuaries who use the latest technology to try to predict the risks associated with any given group of potential insureds. The resulting statistical information might be quite valuable to a competing insurance company. Even a customer contact list has a certain inherent value.
Thus, as you work in the computer security field, always keep in mind that any data that might have economic value is an asset to your organization and that such data provides an attractive target for any competitors who may not have ethical inhibitions against using espionage. If your company management thinks that this threat is not real, then they are very much mistaken. Any company is a potential victim of corporate espionage. You should take steps to protect your valuable information—and the first critical step in this process is asset identification.
Asset identification is the process of listing the assets that you believe support your organization. This list should include things that impact direct day-to-day operations as well as those that are tied to your company’s services or products. The CERT website offers a very useful worksheet that you can use to itemize the assets in your organization.5 This workbook includes a number of other useful worksheets for assuring information security within your organization. As the table of contents in Figure 7.1 shows, this workbook is also a tutorial that steps you through the various considerations in information security.
5. https://www.us-cert.gov/sites/default/files/c3vp/crr_resources_guides/CRR_Resource_Guide-AM.pdf

Figure 7.1 Table of contents from the CERT Supplemental Resource Guide.
Table 7.1 is a variation on the worksheet provided by CERT. Armed with this table and based on your knowledge and experience with your company, you can complete an asset identification by following the steps outlined below:
Table 7.1 Asset Identification Worksheet
Information | Systems | Services and Applications | Other Assets |
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
In the first column of the table, list the information assets. You should list the types of information used by people in your company—the information people need to do their jobs. Examples are product designs, software programs, system designs, documentation, customer orders, and personnel data.
For each entry in the first column, in the second column fill in the names of the systems on which the information resides. In each case, ask yourself which systems people need to perform their jobs.
For each entry in the first column, in the third column fill in the names of the related applications and services. In each case, determine what applications or services are needed for individuals to perform their jobs.
In the last column, list any other assets that may or may not be directly related to the other three columns. Examples are databases with customer information, systems used in production, word processors used to produce documentation, compilers used by programmers, and human resources systems.
Once you complete these steps to fill out Table 7.1, you will have a good understanding of the critical assets for your organization. With this information, you will know how best to devote your defensive efforts. Some specific protective steps will be examined later in this chapter.
Real-World Examples of Industrial Espionage
Now that you have been introduced to the concept of corporate espionage, let’s look at five actual cases. These case studies are of real-world espionage found in various news sources. This section should give you an idea of what types of espionage activities actually occur. Note that while some of these cases are a bit old, they illustrate the way industrial espionage is done. And it is frequently the case that details of an industrial espionage incident do not emerge until many years later, if at all.
Example 1: Hacker Group
Cyber attacks are being used frequently in corporate espionage. From at least November 2018 to well into 2021, the hacking group RedCurl was linked to 30 separate attacks of corporate espionage against companies in the United Kingdom, Germany, Canada, Norway, Russia, and Ukraine. This group tends to favor using its own custom-developed malware and social engineering to gain access to sensitive data.
Example 2: Company Versus Company
In November 2021 Fiat Chrysler Automobiles accused General Motors of corporate espionage. Fiat Chrysler accused GM of impersonating former employees of Fiat Chrysler in emails. GM in turn accused Fiat Chrysler of engaging in bribery and other schemes. The two companies are engaged in multiple lawsuits against each other.
Example 3: Nuclear Secrets
In 2017 Taiwanese-American engineer Allen Ho was sentenced to 2 years in prison for providing nuclear energy technology information to China’s state-owned China General Nuclear Power Company (CGNPC). According to the indictment, Ho, a naturalized American citizen, used his company Energy Technology International, which was based at his home in Wilmington, Delaware, to gather information on the production of nuclear material from American nuclear power developers, including the Tennessee Valley Authority, and pass that information to the CGNPC. Ho engaged in these activities between 1997 and 2016, through his own efforts and those of unnamed consultants he hired.
Example 4: Uber
In 2017 it became public that Uber Technologies Inc. had paid $7 million to keep secret an alleged corporate espionage program. The program allegedly included wiretapping, hacking, bribery, and the use of former intelligence officers, and the industrial espionage team at Uber was named “Threat Operations Unit.” An attorney for former Uber employee Richard Jacob revealed this information in a courtroom.
This information was disclosed in the course of a lawsuit wherein Uber competitor Waymo accused an ex-Uber employee, Anthony Levandowsky, of stealing 14,000 confidential documents and using them to support Uber’s self-driving program. While all the details of this case have not yet been confirmed, the case does illustrate just how extreme industrial espionage can become.
Example 5: Foreign Governments and Economic Espionage
The U.S. government’s National Counterintelligence and Security Center (NCSC) released a 2018 report titled “Foreign Economic Espionage in Cyberspace,”6 which details multiple ways in which foreign governments are conducting economic/industrial espionage against U.S.-based companies.
6. https://www.dni.gov/files/NCSC/documents/news/20180724-economic-espionage-pub.pdf
One area emphasized in the report is the infiltration of the software supply chain. Backdoors in some software allow access to corporate resources. The report also noted that some nations, such as China, have laws that require companies doing business in China to submit their technology to the Chinese government for security reviews. The report alleged that in some cases, these reviews were a pretense to provide Chinese companies with access to technology from Western companies.
As a case in point, in April 2022 Xiang Haitao was sentenced after pleading guilty to conspiring to commit economic espionage.7 He admitted to being part of a plot to deliver software related to soil nutrient applications to the Chinese government. Haitao had worked as a scientist for Monsanto, which developed software designed to help increase productivity for farmers. The software included a proprietary predictive algorithm to help farmers optimize crop nutrients.
7. https://www.newsweek.com/chinese-spy-economic-espionage-stealing-trade-secrets-1696201
Trends in Industrial Espionage
While the cases just discussed range over a number of years, the problem is not abating. In fact, according to a CNN report, 2015 saw a 53% increase in cases of industrial espionage. The FBI conducted a survey of 165 companies and found that half of those companies had been victims of industrial espionage of some type. A significant number of industrial espionage cases involve insider threats.
Industrial Espionage and You
The industrial espionage cases notwithstanding, most companies will deny involvement in anything that even hints at espionage. However, not all companies are quite so shy about the issue. Larry Ellison, CEO of Oracle Corporation, has openly defended his decision to hire private investigators to sift through Microsoft garbage in an attempt to garner information. Clearly, espionage is no longer a problem just for governments and defense contractors. It is a very real concern in the modern business world. A savvy computer security professional will be aware of this concern and will take the appropriate proactive steps.
How Does Espionage Occur?
There are two ways that espionage can occur. An easy, low-technology avenue would be for current or former employees to simply take the data or for someone to use social engineering methods (discussed in Chapter 3, “Cyber Stalking, Fraud, and Abuse”) to extract data from unsuspecting company employees. The second, more technology-oriented method is for individuals to use spyware, which includes the use of cookies and key loggers. There are also other technological methods we will discuss.
Low-Tech Industrial Espionage
Corporate espionage can occur without the benefit of computers or the Internet. Disgruntled former (or current) employees can copy sensitive documents, divulge corporate strategies and plans, or perhaps reveal sensitive information. In fact, whether the method used is technological or not, disgruntled employees are the single greatest security risk to any organization. A corporate spy need not hack into a system in order to obtain sensitive and confidential information if an employee is willing to simply hand over the information. Just as with military and political espionage, the employees’ motives for divulging information vary. Some engage in such acts for obvious financial gains. Others may elect to reveal company secrets merely because they are angry about some injustice (real or imagined). Whatever the motive, any organization has to be cognizant of the fact that it has any number of employees who may be unhappy with some situation and have the potential to divulge confidential information.
Certainly, one can obtain information without the benefit of modern technology; however, computer technology (and various computer-related tactics) can certainly assist in corporate espionage, even if only in a peripheral manner. Some incidents of industrial espionage are conducted with technology that requires little skill on the part of the perpetrator, as illustrated in Figures 7.2 and 7.3. This technology can include using universal serial bus (USB) flash drives, compact discs (CDs), or other portable media to take information out of the organization. Even disgruntled employees who wish to undermine the company or make a profit for themselves will find it easier to burn a wealth of data onto a CD and carry that out in their coat pocket rather than attempt to photocopy thousands of documents and smuggle them out. And the new USB flash drives, smaller than your average key chain, are a dream come true for corporate spies. These drives can plug into any USB port and store a tremendous amount of data. As of this writing, one can easily purchase small portable devices capable of holding 10TB or more of data.

Figure 7.2 Low-tech espionage is easy.

Figure 7.3 Low-tech espionage is portable.
While information can be taken from your company without overt hacking of the system, you should keep in mind that if your system is unsecured, it is entirely possible that an outside party could compromise your system and obtain that information without an employee as an accomplice. In addition to these methods, other low-tech and even virtually “no-tech” methods can be used to extract information. Social engineering, which was discussed at length in Chapter 3, is the process of talking a person into giving up information she otherwise would not divulge. This technique can be applied to industrial espionage in a number of ways.
The first and most obvious use of social engineering in industrial espionage is in direct conversation in which the perpetrator attempts to get the targeted employee to reveal sensitive data. As illustrated in Figure 7.4, employees will often inadvertently divulge information to a supplier, vendor, or salesperson without thinking the information is important or realizing that it could be given to anyone. The attacker simply needs to try to get the target to talk more than she should. In May 2022 various intelligence agencies were warning of foreign spies using social media to begin social engineering attempts.8 A foreign spy might set up a fake profile pretending to be a scientist in order to befriend scientists working on sensitive or classified projects. The goal is to first make contact with the target and then, over time, ingratiate oneself with the target and eventually get access to sensitive data.
8. https://buse.de/en/blog-en/labor-law/cybersecurity-geheimdienste-warnen-vor-industriespionage-ueber-social-media/

Figure 7.4 Social engineering can be used as low-tech espionage.
Another interesting way of using social engineering is via email. In very large organizations, one cannot know every employee, so a clever industrial spy could send an email message claiming to come from some other department and perhaps simply asking for sensitive data. A corporate spy might, for example, forge an email to appear to be coming from the legal office of the target company requesting an executive summary of some research project.
Computer security expert Andrew Briney says that people are the number-one issue in computer security.
Spyware Used in Industrial Espionage
Clearly, any software that can monitor activities on a computer can be used in industrial espionage. An April 2021 article describes a marketplace named Industrial Spy that is set up for the purpose of buying and selling trade secrets. Often, the attackers will first hold the data for ransom and then sell the data—sometimes even if the ransom is paid.9 One method to accomplish monitoring is via spyware, which we discussed in detail in Chapter 5, “Malware.” Clearly, software or hardware that logs keystrokes or takes screenshots would be advantageous to an industrial spy. An August 2021 article specifically discussed an incident wherein the Amazon CEO, Jeff Bezos, had his smart phone targeted by spyware and several megabytes of data exfiltrated over several months. The specific spyware is alleged to have been Pegasus, which was originally created by an Israeli company for government use.
9. https://www.blackfog.com/industrial-spy-selling-stolen-data-to-competitors/
The application of this type of software to espionage is obvious: A spy could get screenshots of sensitive documents, capture logon information for databases, or capture a sensitive document as it is being typed. Any of these methods would give a spy unfettered access to all data that is processed on a machine that contains spyware.
Steganography Used in Industrial Espionage
Steganography is a way of keeping messages secret. Rather than hide messages by using encryption, steganography protects communications by obscuring them. Messages are hidden within images. And in some cases other images are hidden within images. The word steganography comes from the Greek steganos, meaning “covered” or “secret,” and graphy, meaning “writing” or “drawing.” There are several technical means to accomplish this, but the most common is to conceal the data in the least significant bits of an image file. However, data can be concealed in any sort of digital file.
It should also be noted that historically there have been nontechnical means of hiding messages. A few notable examples include the following:
 The ancient Chinese wrapped notes in wax and swallowed them for transport.
The ancient Chinese wrapped notes in wax and swallowed them for transport. In ancient Greece, a messenger’s head would be shaved, a message was written on his head, and then his hair was allowed to grow back.
In ancient Greece, a messenger’s head would be shaved, a message was written on his head, and then his hair was allowed to grow back. In 1518, Johannes Trithemius wrote a book on cryptography and described a technique in which a message was hidden by having each letter taken as a word from a specific column.
In 1518, Johannes Trithemius wrote a book on cryptography and described a technique in which a message was hidden by having each letter taken as a word from a specific column.
You might think that accomplishing steganography requires a great deal of technical knowledge; however, there are many software packages available that will perform steganography for you. Quick-Stego and Invisible Secrets are two very easy-to-use software tools that will do steganography for you. MP3Stego is a free tool that hides data inside MP4 files. These are just a few of the tools available on the Internet. The widespread availability of cheap or free tools that are easy to use makes steganography a threat to any organization.
Phone Taps and Bugs
Of course, there is always the possibility of using phone taps. A phone tap involves tying into a phone line at some point and intercepting calls. This is often done at some utility location inside the building one wishes to tap. Obviously, this sort of attack requires the attacker to enter on or near the premises, compromise phone equipment, and have the skill to tap into the phone line.
Spy for Hire
A 2021 article discussed mercenary spy firms, which are private surveillance companies.10 Many of these companies claim to engage only in legitimate work; however, many have been accused of illegal activities. The company Black Cube, for example, deployed spies on behalf of Harvey Weinstein. Similar information was published in a 2021 Tech Republic article,11 which discusses a report that identified six companies: Cobwebs Technologies, Cognyte, Black Cube, Bluehawk CI, BellTroX, and Cytrox, as well as an unnamed group in China.12
10. https://www.reuters.com/technology/facebook-exposes-mercenary-spy-firms-that-targeted-48000-people-2021-12-16/
11. https://www.techrepublic.com/article/surveillance-for-hire-are-you-a-target-of-the-booming-spy-business/
12. https://about.fb.com/wp-content/uploads/2021/12/Threat-Report-on-the-Surveillance-for-Hire-Industry.pdf
Industrial espionage can involve a disgruntled insider or spyware; however, it can also involve “spies for hire” (that is, mercenary spies). These individuals are usually experienced investigators, and sometimes they’re even former employees of intelligence agencies. This means that one should not be surprised to see the same techniques and tools that nation-states use now used in industrial espionage.
A 2022 article in the New York Post describes specifically how one former corporate spy gathered data.13 His techniques relied primarily on social engineering, and his tools were nothing more than a phone and his laptop. Robert Kerbeck, the spy in question, claims to have been earning up to $2 million per year doing corporate espionage.
13. https://nypost.com/2022/03/09/ex-corporate-spy-robert-kerbeck-on-how-he-got-companies-info/
Protecting Against Industrial Espionage
By now, you are aware that there are many ways that your organization’s valuable information assets can be compromised. What steps can you take to alleviate the danger? Note that I said alleviate the danger. There is nothing you can do to make any system, any information, or any person totally secure. Totally unbreakable security is simply unattainable. The best you can do is work to achieve a level of security that makes the effort required to get information more costly than the value of the information.
One obvious protection is to employ antispyware software. As mentioned earlier in this book, many antivirus programs also have antispyware capabilities. This software, coupled with other security measures, such as firewalls and intrusion detection software (examined in Chapter 9, “Computer Security Technology”), should drastically reduce the chance that an outside party will compromise your organization’s data. Furthermore, implementing organizational policies (also discussed in Chapter 9) that help guide employees on safely using computer and Internet resources will make your system relatively secure. If you add to your protection arsenal the strategy of encrypting all transmissions, your system will be as secure as you can reasonably make it. (Chapter 8, “Encryption,” is devoted to encryption.) However, all of these techniques—firewalls, company policies, antispyware, encryption, and so forth—will only help in cases in which the employee is not the spy. What do you do to ameliorate the danger of employees intentionally stealing or compromising information? Actually, there are several courses of action any organization can take to reduce risks due to internal espionage. Here are 12 measures you can use:
 Always use all reasonable network security: firewalls, intrusion detection software, antispyware, patches and updates for the operating system, and proper usage policies.
Always use all reasonable network security: firewalls, intrusion detection software, antispyware, patches and updates for the operating system, and proper usage policies. Give the personnel of the company access to only the data that they absolutely need to perform their jobs. This concept is referred to as least privileges. The employees are given the minimum privileges necessary to perform their job tasks. Use a need-to-know approach. One does not want to stifle discussion or exchange of ideas, but sensitive data must be treated with great care.
Give the personnel of the company access to only the data that they absolutely need to perform their jobs. This concept is referred to as least privileges. The employees are given the minimum privileges necessary to perform their job tasks. Use a need-to-know approach. One does not want to stifle discussion or exchange of ideas, but sensitive data must be treated with great care. If possible, set up a system for those employees with access to the most sensitive data in which there is a rotation or a separation of duties. Ensure that no one employee has access and control over all critical data at one time.
If possible, set up a system for those employees with access to the most sensitive data in which there is a rotation or a separation of duties. Ensure that no one employee has access and control over all critical data at one time. Limit the number of portable storage media in the organization (such as CD burners and flash drives) and control access to these media. Log every use of such media and what was stored. Some organizations have even prohibited cell phones because most phones allow the user to photograph items and send the pictures electronically.
Limit the number of portable storage media in the organization (such as CD burners and flash drives) and control access to these media. Log every use of such media and what was stored. Some organizations have even prohibited cell phones because most phones allow the user to photograph items and send the pictures electronically. Do not allow employees to take documents/media home. Bringing materials home may indicate a very dedicated employee working on her own time or a corporate spy copying important documents and information.
Do not allow employees to take documents/media home. Bringing materials home may indicate a very dedicated employee working on her own time or a corporate spy copying important documents and information. Shred documents and melt old disks/tape backups/CDs. A resourceful spy can often find a great deal of information in the garbage. If any storage media is disposed of, it should be completely wiped. Degaussing is a good technique for hard drives and USB drives.
Shred documents and melt old disks/tape backups/CDs. A resourceful spy can often find a great deal of information in the garbage. If any storage media is disposed of, it should be completely wiped. Degaussing is a good technique for hard drives and USB drives. Do employee background checks. You must be able to trust your employees, and you can only do this with a thorough background check. Do not rely on “gut feelings.” Give particular attention to information technology (IT) personnel who will, by the nature of their jobs, have access to a wide variety of data. This scrutiny is most important with positions such as database administrators, network administrators, and network security specialists.
Do employee background checks. You must be able to trust your employees, and you can only do this with a thorough background check. Do not rely on “gut feelings.” Give particular attention to information technology (IT) personnel who will, by the nature of their jobs, have access to a wide variety of data. This scrutiny is most important with positions such as database administrators, network administrators, and network security specialists. When any employee leaves the company, scan the employee’s PC carefully. Look for signs that inappropriate data was kept on that machine. If you have any reason to suspect inappropriate usage, then store the machine for evidence in subsequent legal proceedings.
When any employee leaves the company, scan the employee’s PC carefully. Look for signs that inappropriate data was kept on that machine. If you have any reason to suspect inappropriate usage, then store the machine for evidence in subsequent legal proceedings. Keep all tape backups, sensitive documents, and other media under lock and key and allow limited access to them.
Keep all tape backups, sensitive documents, and other media under lock and key and allow limited access to them. If portable computers are used, then encrypt the hard drives. Encryption prevents a thief from extracting usable data from a stolen laptop. A number of products on the market can accomplish this encryption, including the following:
If portable computers are used, then encrypt the hard drives. Encryption prevents a thief from extracting usable data from a stolen laptop. A number of products on the market can accomplish this encryption, including the following: VeraCrypt (see Figure 7.5) is one example of a free tool for encrypting drives, folders, or partitions. The tool is remarkably easy to use and can be found at https://www.veracrypt.fr.
VeraCrypt (see Figure 7.5) is one example of a free tool for encrypting drives, folders, or partitions. The tool is remarkably easy to use and can be found at https://www.veracrypt.fr.There are several other similar tools, most of which are low cost or free.
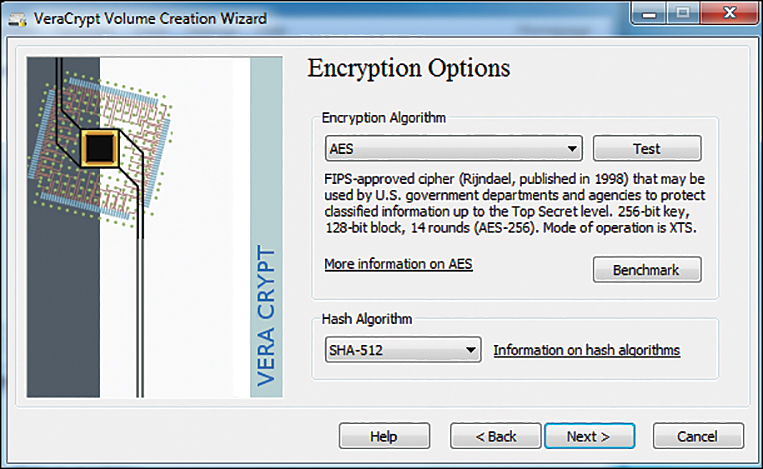
Figure 7.5 VeraCrypt.
 Microsoft Windows includes two types of encryption. Windows 7 Enterprise or Ultimate editions included BitLocker for encrypting entire hard drives. BitLocker is also available on later versions of Windows (8, 8.1, 10, 11). And all versions of Windows since Windows 2000 have included Encrypted File System for encrypting specific files or folders (see Figure 7.6).
Microsoft Windows includes two types of encryption. Windows 7 Enterprise or Ultimate editions included BitLocker for encrypting entire hard drives. BitLocker is also available on later versions of Windows (8, 8.1, 10, 11). And all versions of Windows since Windows 2000 have included Encrypted File System for encrypting specific files or folders (see Figure 7.6). DiskCryptor is an open-source drive encryption application. It supports algorithms such as AES and Serpent (which you will learn more about in Chapter 8). DiskCryptor can encrypt external devices such as USB and DVD devices. It is available from https://diskcryptor.org.
DiskCryptor is an open-source drive encryption application. It supports algorithms such as AES and Serpent (which you will learn more about in Chapter 8). DiskCryptor can encrypt external devices such as USB and DVD devices. It is available from https://diskcryptor.org.
This list is not exhaustive; therefore, it is highly recommended that you carefully review a variety of encryption products before making a selection.
 Have all employees with access to any sensitive information sign nondisclosure agreements. Such agreements give an employer recourse in the event that an ex-employee divulges sensitive data. It is amazing how many employers do not bother with this rather simple protection. Use of nondisclosure agreements is the primary means of protecting trade secrets.
Have all employees with access to any sensitive information sign nondisclosure agreements. Such agreements give an employer recourse in the event that an ex-employee divulges sensitive data. It is amazing how many employers do not bother with this rather simple protection. Use of nondisclosure agreements is the primary means of protecting trade secrets. Conduct security awareness sessions. Clearly, employee education is one of the most important things you can do. An organization should have some method for routinely advising employees about security issues. An excellent way to do that is to have an intranet site with bulletins posted to it. It is also a good idea to hold periodic training sessions for employees. These need not be lengthy or in depth. Most nontechnical employees only need an introduction to security concepts.
Conduct security awareness sessions. Clearly, employee education is one of the most important things you can do. An organization should have some method for routinely advising employees about security issues. An excellent way to do that is to have an intranet site with bulletins posted to it. It is also a good idea to hold periodic training sessions for employees. These need not be lengthy or in depth. Most nontechnical employees only need an introduction to security concepts.
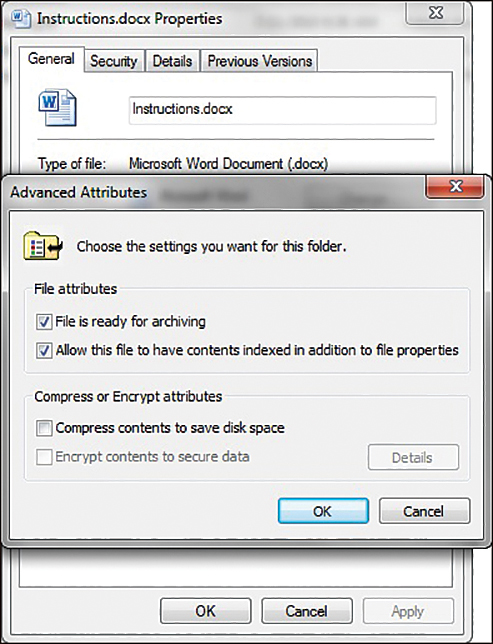
Figure 7.6 Windows EFS.
Unfortunately, taking these simple measures will not make you totally immune to corporate espionage. However, using these strategies will make any such attempts much more difficult for any perpetrator; thus, you will improve your organization’s data security.
Trade Secrets
Trade secrets were briefly mentioned previously in this chapter; however, this topic deserves a bit more detailed discussion. This author has been involved as an expert witness in multiple trade secrets misappropriation cases. One of the defenses that is used against allegations of trade secret misappropriation is that the trade secret was not identified. At a minimum, you should mark documents confidential; you should preferably mark trade secrets as such. It is possible a court will still uphold that something without such markings is a trade secret, particularly if the information is something a reasonable person should know is a trade secret. Appropriately marking information, however, removes any ambiguity.
The second defense against allegations of trade secret misappropriation is often that the data was not secured properly. Essentially, the concept is that if one truly views something as a trade secret, then it will be guarded more closely than other data.
The journal CSO recommended several possible choices for protecting trade secrets:14
14. https://www.csoonline.com/article/3268810/protecting-trade-secrets-technology-solutions-you-can-use.html
Once data has been classified and labelled, there are a wide range of possible protection choices, depending on your use cases. These could include ERMS (Enterprise Rights Management System) persistent encryption, file encryption, document passwords, etc.
Document passwords are one of the options that CSO lists for protecting trade secrets. It should also be noted that CSO does not suggest an organization must implement all of the choices but rather select from the choices those that are a good fit for the organization. Document passwords are well suited for protecting confidential data in a document.
The U.S. Small Business Administration recommends even less substantial security measures, such as simply locking trade secrets in a cabinet (if it is a paper copy) or limiting access to files on a computer:15
15. https://sba.thehartford.com/business-management/business-questions/keep-trade-secrets-safe/
2. Keep Trade Secrets Confidential
Identification is only step one; reasonable efforts for protection are step two. You don’t have to keep your secrets in Fort Knox to protect them; marking them “confidential” and keeping them out of the public eye is sufficient because it is reasonable under the circumstances. But merely stamping “confidential” on a piece of paper won’t protect a trade secret if you don’t treat the paper like a secret worth keeping.
 For trade secrets on paper: keep them stored in a locked file cabinet
For trade secrets on paper: keep them stored in a locked file cabinet For trade secrets on computer: limit access to the electronic files
For trade secrets on computer: limit access to the electronic files
Limiting access to files on a computer is accomplished via passwords for the computer. It is further enhanced if one also has the document password protected. It can be further enhanced with file or drive encryption, but this is not required.
A symposium by attorneys on protecting trade secrets made the following comments on security of trade secrets:16
16. https://www.foley.com/files/uploads/AIPLA%20Article%20on%20DTSA%20and%20Reasonable%20Efforts%20to%20Protect%20Trade%20Secrets%2048.pdf
Reasonable Efforts to Protect Trade Secrets
To be protectable as a trade secret, a plaintiff must prove that the trade secret is information that derives economic value (actual or potential) because it is not generally known and that such information is the subject of reasonable efforts to maintain its secrecy. Often the toughest aspect of a plaintiff’s trade secret action is proving that the trade secret was the subject of “reasonable efforts” to maintain its secrecy. The secrecy requirement has been shown or fulfilled in many ways, including by:
 Restricting access to the information (e.g., locking it away in a secure place such as a vault or via computer or network security);
Restricting access to the information (e.g., locking it away in a secure place such as a vault or via computer or network security); Limiting the number of people who know the information;
Limiting the number of people who know the information; Having the people who know, or who come into contact with the trade secret, directly or indirectly, agree in writing not to disclose the information (e.g., sign non-disclosure agreements (in the case of third parties) or confidentiality or employment agreements (in the case of employees and consultants/contractors)); and/or
Having the people who know, or who come into contact with the trade secret, directly or indirectly, agree in writing not to disclose the information (e.g., sign non-disclosure agreements (in the case of third parties) or confidentiality or employment agreements (in the case of employees and consultants/contractors)); and/or Marking any written material pertaining to the trade secret as confidential and proprietary and following up (as practical) in writing if verbal disclosure.
Marking any written material pertaining to the trade secret as confidential and proprietary and following up (as practical) in writing if verbal disclosure.
The Contracting Excellence Journal has the following to say about protecting trade secrets:17
17. https://journal.iaccm.com/contracting-excellence-journal/protect-your-trade-secrets-using-cybersecurity
1. Identity and access management
Courts so far have looked at some very basic forms of identity and access protection in trade secrets cases including password protection, “need to know” access and secure server storage.
2. Data security measures
Particular cybersecurity protections that deal with how confidential data may or may not be stored or transferred have been cited in a few cases as important “reasonable efforts” in protecting trade secrets, for example, USB use restrictions and electronic and physical distribution controls.
3. Perimeter and network defenses
Attempts to access a company’s trade secrets by competitors, “hacktivists,” malicious ex-employees, and even nation-states, can take the form of hacking of the company’s external networks or internal equipment. Evidence of “reasonable steps” taken to prevent this kind of trade-secret theft include firewalls, data encryption and online use restrictions.
4. Communication
Companies’ communications with training of their employees in cybersecurity and other aspects of trade-secret protection are vital best practices. A few courts have recognized certain types of electronic communications to employees as helpful “reasonable efforts,” for example, pop-up warning indicating potential risks.
5. Monitoring
Cybersecurity is obviously not just a one-time exercise in putting particular protections in place for all time, but an effort that needs to be monitored, measured and improved over time. Courts have started to recognize some elements of ongoing cybersecurity monitoring as relevant for protecting trade secrets, for example, email monitoring.
This article outlines cybersecurity measures that are reasonable for protecting trade secrets. Use of firewalls, some level of data encryption, some level of access control, and restricting access are the essentials of their recommendations.
The Industrial Espionage Act
The Industrial Espionage Act of 1996 was the first U.S. law to criminalize theft of commercial trade secrets. This law provides for significant penalties for violators. The following wording is quoted from the law:18
18. https://irp.fas.org/congress/1996_rpt/s104359.htm
(a) Whoever, with intent to convert a trade secret, that is related to or included in a product that is produced for or placed in interstate or foreign commerce, to the economic benefit of anyone other than the owner thereof, and intending or knowing that the offense will injure any owner of that trade secret, knowingly—
(1) steals, or without authorization appropriates, takes, carries away, or conceals, or by fraud, artifice, or deception obtains such information;
(2) without authorization copies, duplicates, sketches, draws, photographs, downloads, uploads, alters, destroys, photocopies, replicates, transmits, delivers, sends, mails, communicates, or conveys such information;
(3) receives, buys, or possesses such information, knowing the same to have been stolen or appropriated, obtained, or converted without authorization;
(4) attempts to commit any offense described in paragraphs (1) through (3); or
(5) conspires with one or more other persons to commit any offense described in paragraphs (1) through (3), and one or more of such persons do any act to effect the object of the conspiracy, shall, except as provided in subsection (b), be fined under this title or imprisoned not more than 10 years, or both.
Spear Phishing
Phishing, as you know, is the process of attempting to get personal information from a target in order to steal the target’s identity or compromise the target’s system. A common technique is to send out a mass email that is designed to entice recipients to click on a link that purports to be some financial institution’s website but is actually a phishing website.
Spear phishing uses the same technology as phishing but in a targeted manner. For example, if an attacker wanted to get into the servers at a defense contractor, he might craft email and phishing websites specifically to target software and network engineers at that company. The emails might be made to appeal to that specific subgroup of people. Or the attacker might even take the time to learn personal details of a few of these individuals and target them specifically. This technique has been used against executives at various companies. In 2010 and 2011, this problem began to grow significantly.
Whaling is a form of phishing in which an attacker attempts to compromise information regarding a specific highly valuable employee. It involves the same techniques as phishing but is highly customized to increase the chances that the single individual target will be fooled and actually respond to the phishing attempt.
Summary
A number of conclusions can be drawn from this chapter’s examination of industrial espionage. The first conclusion: It does indeed occur. The case studies clearly demonstrate that industrial espionage is not some exotic fantasy dreamed up by paranoid security experts. It is an unfortunate, but quite real, aspect of modern business. If your firm’s management chooses to ignore these dangers, then they do so at their own peril.
The second thing that can be concluded from this brief study of industrial espionage is that there are a variety of methods by which espionage can take place. An employee revealing confidential information is perhaps the most common. However, compromising information systems is another increasingly popular means of obtaining confidential and potentially valuable data. You will want to know the best way to protect your company and yourself. In the upcoming exercises, you will run screen-capture software, key loggers, and antispyware so you can learn more about espionage tactics and how to deal with them.
Test Your Skills
Multiple Choice Questions
1. Terrance is trying to explain industrial espionage to a group of new security techs. What is the ultimate goal of espionage?
A. To subvert a rival government
B. To obtain information that has value
C. To subvert a rival business
D. To obtain information not otherwise available
2. In order to truly understand industrial espionage, you need to understand the mindset of the spy. What is the best outcome for a spy attempting an espionage activity?
A. To obtain information without the target even realizing he did so
B. To obtain information with or without the target realizing he did so
C. To obtain information and discredit the target
D. To obtain information and cause harm to the target
3. What is the usual motivating factor for corporate/industrial espionage?
A. Ideological
B. Political
C. Economic
D. Revenge
4. Which of the following types of information would be a likely target for industrial espionage?
A. A new algorithm that the company’s IT department has generated
B. A new marketing plan that the company has formulated
C. A list of all the company’s customers
D. All of these answers are correct
5. Accurate statistics on corporate espionage are difficult to obtain. One reason is that the victims don’t always report the crime, as they often don’t want the incidents to become public. Which of the following is a likely reason that an organization might be reluctant to admit it has been a victim of corporate espionage?
A. It would embarrass the IT department.
B. It would embarrass the CEO.
C. It might cause stock value to decline.
D. It might lead to involvement in a criminal prosecution.
6. What is the difference between corporate and industrial espionage?
A. None; they are interchangeable terms.
B. Industrial espionage only refers to heavy industry, such as factories.
C. Corporate espionage only refers to executive activities.
D. Corporate espionage only refers to publicly traded companies.
7. Information is a valuable asset. It can be useful to calculate that value in order to determine how much effort should be put into protecting it. What formula can you use to calculate the value of information?
A. Resources needed to produce the information plus resources gained from the information
B. Resources needed to produce the information multiplied by resources gained from the information
C. Time taken to derive the information plus money needed to derive the information
D. Time taken to derive the information multiplied by money needed to derive the information
8. If a company purchases a high-end UNIX server to use for its research and development department, what is probably the most valuable part of the system?
A. The high-end UNIX server
B. The information on the server
C. The devices used to protect the server
D. The room to store the server
9. Information is an asset to your company if it
A. cost any sum of money to produce.
B. cost a significant sum of money to produce.
C. might have economic value.
D. might cost significant money to reproduce.
10. What is the greatest security risk to any company?
A. Disgruntled employees
B. Hackers
C. Industrial spies
D. Faulty network security
11. Which of the following is the best definition for spyware?
A. Software that assists in corporate espionage
B. Software that monitors activity on a computer
C. Software that logs computer keystrokes
D. Software that steals data
12. What is the highest level of security you can expect to obtain?
A. A level of security that makes the effort required to get information more costly than the value of the information
B. A level of security comparable with government security agencies, such as the Central Intelligence Agency
C. A level of security that has a 92.5% success rate in stopping intrusion
D. A level of security that has a 98.5% success rate in stopping intrusion
13. In the context of preventing industrial espionage, why might you wish to limit the number of company CD burners and control access to them in your organization?
A. An employee could use such media to take sensitive data.
B. An employee could use such media to copy software from the company.
C. CDs could be a vehicle for spyware to get on your system.
D. CDs could be a vehicle for a virus to get on your system.
14. Why would you want to scan an employee’s computer when he leaves the organization?
A. To check the workflow prior to his leaving
B. To check for signs of corporate espionage
C. To check for illegal software
D. To check for pornography
15. What is the reason for encrypting hard drives on laptop computers?
A. To prevent a hacker from reading the data while you are online
B. To ensure that data transmissions are secure
C. To ensure that another user on that machine will not see sensitive data
D. To prevent a thief from getting data off of a stolen laptop
Exercises
EXERCISE 7.1: Learning About Industrial Espionage
Using the Web, library, journals, or other resources, look up a case of industrial or corporate espionage that was not already mentioned in this chapter.
Write a brief essay describing the facts in the case. The parties in the case and the criminal proceeding are of interest, but most of your discussion should focus on the technical aspects of the case. Be sure to explain how the espionage was conducted.
EXERCISE 7.2: Using Antispyware
Note that this exercise may be repeated with different antispyware products. It is a good idea for any person interested in computer security to be familiar with multiple antispyware products.
Go to the website of one of the antispyware utilities. (See Chapter 5 if you need more direction.)
Find instructions on the vendor’s website.
Download the trial version of that software.
Install the software on your machine.
After installation, run the utility. What did it find? Record your results.
Let the utility remove or quarantine anything it found.
EXERCISE 7.3: Learning About Key Loggers
Note that this exercise may only be completed on machines where you have explicit permission to do so (not on public computers).
Using any website, find and download a key logger. The following websites might help you locate a key logger: www.kmint21.com/familykeylogger/ and www.blazingtools.com/bpk.html.
Install the key logger on your PC.
Examine how the key logger behaves on your machine. Do you notice anything that might indicate the presence of illicit software?
Run the antispyware software you downloaded in Exercise 7.2. Does the antispyware software detect the key logger?
EXERCISE 7.4: Screen-Capture Spyware
Using the Web, find and download a screen-capturing spyware application. The following website might be helpful to you in selecting an appropriate product: http://en.softonic.com/s/screen-capture-spy-software. Warning: Since you are downloading spyware, it is likely that your system’s antivirus/antispyware will give you a warning.
Install and configure the application on your computer.
Run the application and note what it finds.
Run the antispyware from Exercise 7.2 and see whether it detects your spyware program.
EXERCISE 7.5: Learning About Hardware-Based Key Loggers
In this chapter, as well as in Chapter 5, we discussed software-based key loggers. However, there are also hardware-based key loggers.
Use the Internet to learn more about hardware-based key loggers. (You may wish to search for “KEYKatcher” as a starting point.)
Write an essay outlining the way in which these key loggers work and how they could be implemented for either security or industrial espionage.
Projects
PROJECT 7.1: Preventing Corporate Espionage
Using one of the websites listed in this book (you can also choose from the preferred resources in Chapter 1) or other resources, find a set of guidelines on general computer security. Write a brief essay comparing and contrasting those guidelines against the ones given in this chapter. Keep in mind that the guidelines in this chapter relate specifically to corporate espionage and not to general computer security.
PROJECT 7.2: Handling Employees
Write a brief essay describing steps regarding the handling of employees. Include all steps that you believe an organization should take to prevent corporate espionage. It is important that you support your opinions with sources and reasons.
If possible, visit a company and talk with someone in either the IT department or personnel department to learn how that company handles issues such as employee termination, rotation of duties, control of access to data, and so forth. Compare and contrast the measures you wrote about in your essay to those used by the company you visited.
PROJECT 7.3: Asset Identification in Your Organization
Using Table 7.1 or a similar asset identification table of your own design, identify the most valuable data in your organization (school or business) and what parties would most likely wish to access that data. Then write a brief guideline on how you might go about securing that data. In this project, you should tailor your security recommendations to the specific type of data you are trying to protect and against the most likely perpetrators of industrial espionage.
Case Study
David Doe is a network administrator for the ABC Company. David is passed over for promotion three times. He is quite vocal in his dissatisfaction with this situation. In fact, he begins to express negative opinions about the organization in general. Eventually, David quits and begins his own consulting business. Six months after David’s departure, it is discovered that a good deal of the ABC Company’s research has suddenly been duplicated by a competitor. Executives at ABC suspect that David Doe has done some consulting work for this competitor and may have passed on sensitive data. However, in the time since David left, his computer has been formatted and reassigned to another person. ABC has no evidence that David Doe did anything wrong. Consider the following questions:
What steps might have been taken to detect David’s alleged industrial espionage?
What steps might have been taken to prevent his perpetrating such an offense?
