A malware report is only useful if the people with the power to address an issue can access the report. One of the paradigms of integrating your anti-virus with SCCM is the fact that many more people in an organization will now need access to SCCM. While the new role-based privileges alleviate this pain point somewhat, there will likely be some individuals with whom you just are not comfortable giving access to the SCCM console,who will need to access SCEP reporting data.
Luckily, this can be addressed by granting them access to the SCEP reports within SQL Reporting Services. This recipe will walk you through the procedure for doing so.
For this recipe, you will need to utilize an account that has administrator privileges for the SQL Reporting Services instance that is hosting your SCCM reports. This recipe is written from the perspective of being logged into the server that is hosting the reports and running IE locally. The procedure can also be done remotely; just replace localhost with the DNS name of the server.
In order to be able to deliver report subscriptions over email, it is required that the SMTP information has been entered into the SQL Reporting Services Configuration Utility and that the corresponding Exchange server allows for the SQL reporting services server to send SMTP traffic through its SMTP connector.
Follow these steps:
- Log into SQL Reporting Services server and launch Internet Explorer.
- Browse to the following URL: http://localhost/Reports/Pages/Folder.aspx.
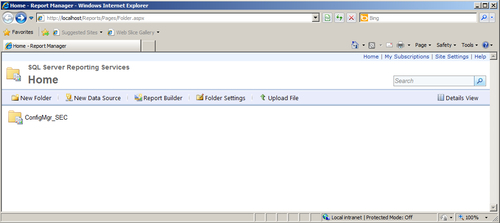
- Proceed to drill down to the directory that hosts your SCEP reports by clicking on
ConfigMgr_XXX(XXX representing your site code) and then selecting theEndpoint Protectiondirectory. - To grant user or group of users access to the reports in the directory, click on the Folder Settings button and then select Security from the left hand-side of the page.

- Next, click on the New Role Assignment button, enter a user or group name in the field provided, and check the boxes for the permissions you wish to grant. At minimum, select the Browser and ConfigMgr Reports Users roles. Click on OK to complete the process.
- Next, we will create a subscription for the Dashboard report, which will deliver it on a scheduled basis over e-mail. Use your browser's back button to return to the root of the Endpoint Protection reports directory.
- Hover your cursor over the link for the Dashboard report for a moment and a gold down arrow icon will appear. Click this and select Subscribe from the drop-down menu.

- Make sure E-mail is selected from the drop-down menu at the top of page. You will need to enter a value for the To: field and supply a reply address (it does not need to be an actual email account).
- Select a render format for the e-mail subscription. The PDF format is typically ideal as it can be easily read on both PCs and mobile devices. Refer to the following screenshot:
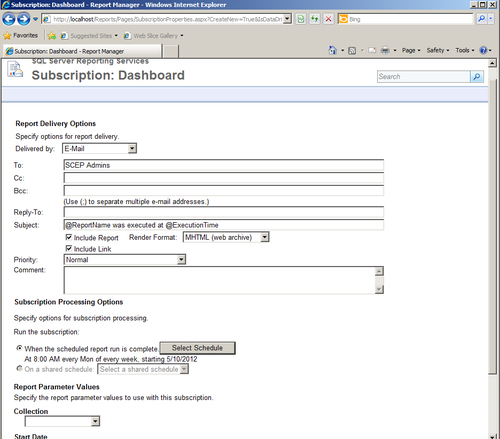
- Next, set a schedule for the report by clicking on the Select Schedule button.
- Finally, select a collection for this report to be run against and click on OK to create the subscription.
SQL Reporting Services provides an ideal platform for SCEP reports, because it allows you easily assign access to an Active Directory user or a group and can be relied upon to deliver reports on a schedule. Keeping your admins from setting up an Outlook rule to automatically place the e-mails in the recycling bin is another matter entirely.
