Certificates are the crucial elements in the security of claims-based applications. They are used for signing and encrypting tokens that are transmitted across the security boundaries, safeguarding the communication from security threats such as man-in-the-middle attacks and eavesdropping.
This recipe shows the concepts of deploying certificates and retrieving them to create the signing credentials and the proof tokens that will be used throughout the course of this book.
To configure the certificates for claims-based applications, perform the following steps:
- Open Visual Studio command prompt in Administrator Mode and run the
makecertcommand:makecert -r -pe -n "CN= SamlTokenSigningCertificate" -b 01/01/2010 -e 01/01/2012 -sky exchange -ss myA self-signed certificate with the
SamlTokenSigningCertificatesubject is generated and stored in theMystore. The private key is marked exportable. - Launch the Management Console window by entering mmc in Windows Run and click on Add/Remove Snap-in under the File menu. Choose the Certificates snap-in and click on Add, as shown in the following screenshot:

- Choose My Account from the prompt, and click on Finish. Click on OK to return to the Management Console window.
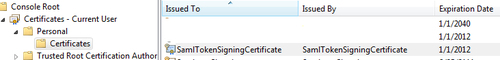
- Expand the Personal folder, and you will find the certificate deployed, as shown in the following screenshot:
- The Certificates snap-in can be used further to copy certificates to the other locations, to export and set permissions.
- Create an
X509CertificateHelperclass and add a static method—GetValidCertificateFromStorethat accepts the subject name, store location, and the valid time as parameters, and returns the X509 certificate from the store:public static X509Certificate2 GetValidCertificateFromStore(StoreLocation location, DateTime timeValid, string subjectDistinguishedName) { X509Store store = new X509Store(location); try { store.Open(OpenFlags.ReadOnly); X509Certificate2Collection validCertificates = store.Certificates.Find(X509FindType.FindByTimeValid, timeValid, false); X509Certificate2Collection signingCertificate = validCertificates.Find(X509FindType.FindBySubjectDistinguishedName, subjectDistinguishedName, false); if (signingCertificate.Count == 0) return null; return signingCertificate[0]; } finally { store.Close(); } }
A collection of the certificates that are valid for the specified date is retrieved and a lookup is performed using the unique subject. The method shown here makes a very target-specific search. There could be overloaded methods that are more generic in nature. An example would be to look for matching (contains string) subjects. The X509FindType.FindBySubjectName search criteria could be used for such purpose. The retrieved certificate will be used to create a digital signature for the token (discussed in the Designing claims-based tokens using Security Assertion Markup Language recipe earlier in this chapter).
You can have a look at the Cryptographic Tasks article at http://msdn.microsoft.com/en-us/library/7yx4d854.aspx to learn more about the cryptographic operations that can be performed using Microsoft CryptoAPI.
A proof token is used by the requestor to authenticate, in order to get GenericXmlSecurityToken from the issuer. A good overview of the proof tokens is provided by Vittorio Bertocci from MSFT in his blog at http://blogs.msdn.com/b/vbertocci/archive/2008/01/02/on-prooftokens.aspx.
