Procedures between UE and EPC Elements
EPS Authentication and Key Agreement (AKA)
The EPS AKA produces keying material forming a basis for the user plane, RRC and the NAS ciphering keys as well as RRC and NAS integrity protection keys.
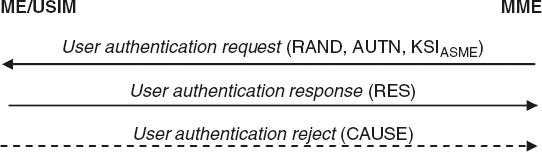
Figure 14.5 EPS Authentication and Key Agreement. Reproduced by permission of © 2010 3GPP. Further use is strictly prohibited.
The MME sends to the USIM a random challenge, an authentication token, in addition to the KASME. The KASME key is a base key, from which NAS keys and KeNB keys and H are derived. The KASME is never transported to an entity outside of the EPC, but KEnb and NH are transported to the eNB from the EPC when the UE transitions to ECM-CONNECTED. From the KeNB, the eNB and UE can derived the UP and RRC Keys.
When the USIM receives the authentication request, as shown in Figure 14.5, it verifies the freshness of the authentication vector and, if acceptable, computes a response. If the verification fails, the ME responds an authentication reject message indicating cause.
Distribution of Authentication Data from HSS to Serving Network
This procedure enables the HSS in the UE's home environment to provide one or authentication vector to the serving network's MME to perform user authentication. The standard recommends that only one EPS authentication vector is fetched due to capability of an elaborate key hierarchy (see below). The authentication data request shall include the IMSI, serving networking identity and the network type. When the HE receives the request, can use either pre-computed or vectors or compute vectors on demand.
User Identification by a Permanent Identity
The user identification mechanism is invoked by the serving network whenever the user cannot be identified by means of a temporary identity, especially when the serving network cannot retry the IMSI based on the GUITI by which the user identifies itself on the radio path.